When I was in high school during the pre-Internet days of the 1980s, I thought that my various classes (along with some excellent teachers) gave us a solid educational foundation, as well as everything we needed (academically) to take on the world. Of course, we did have one colossal advantage back then – all of the information we accessed via our libraries, textbooks, printed encyclopedias, newspapers and TV news anchors was always carefully vetted, edited, revised, peer-reviewed, or fact-checked before it was published or delivered. Our information was of the highest quality, and could always be counted on for accuracy. Of course, we didn’t appreciate (or even realize) it then, because that’s just the way things were; that was normal.
It’s mind-boggling how things have changed since then. In only one generation, the Internet has become woven into the fabric of our daily lives. One of the major benefits of this parallel online world is that information now flows in both directions. In high school, we were simply information consumers; today, anyone can create a web page, publish a blog or post comments to various message boards. We all have a voice; the Internet and social media have placed all of us on a level playing field. This is what sociologists call “the democratization of media”. Overall this is a good thing, because it’s empowering. You no longer need to own (or be employed by) a media company in order to be heard.
Unfortunately, there is also a significant downside to this new freedom. The democratization of media has lowered the barriers to entry so significantly, very little of the contributed and promulgated information is still vetted before it’s published. Any marginally-educated yahoo or axe-grinding misanthrope can now post anything he wants online, and much if it is just utter nonsense.
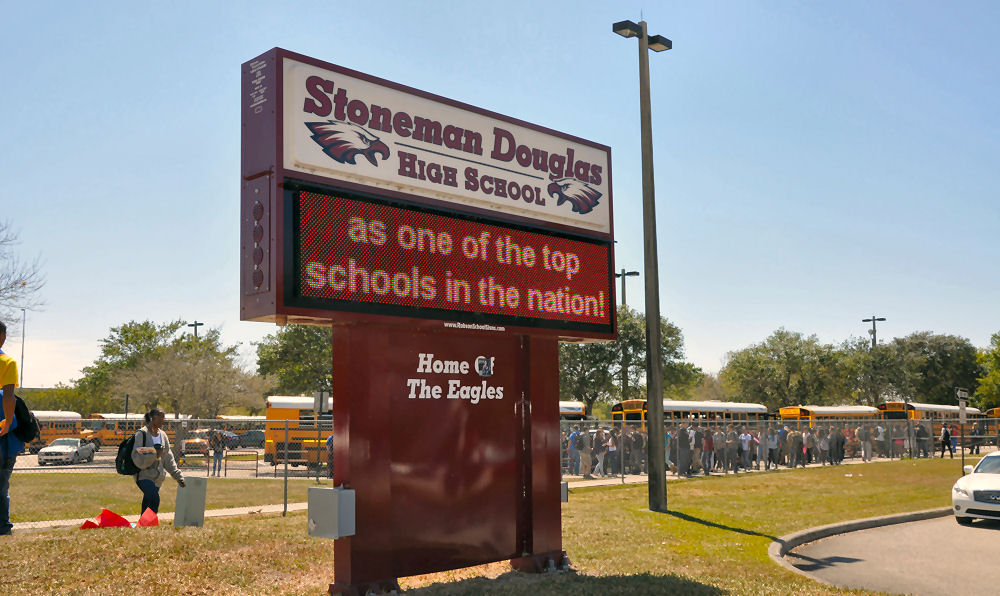
During my time in high school, learning was much like wandering through a museum – we were given only the highest-quality, carefully-vetted information, hand-picked by a legion of curators. Today’s teenagers no longer have that luxury – since most information searches are now done online, and since anyone can be a content creator, their information-gathering experience is more like a garage sale: there are still objects of value, but they are surrounded by heaps of worthless junk and items of dubious provenance; one needs to be exceedingly knowledgeable in order to recognize the valuable merchandise amid the great swaths of detritus.
Today’s teens need well-developed critical thinking skills, so that they can navigate the information superhighway – or, more accurately, the information quagmire. They can’t simply accept and digest what is presented to them, the way that we could when we were their age – they need to investigate, contemplate, question, consider, interpret, analyze, consult… and then formulate their own opinions.
Now, The Bob Angle: my high school education covered all of the bases, but in today’s connected world, the democratization of media and the resulting lack of information vetting has created a cavernous knowledge gap in our educational system. High school students need to develop critical thinking skills now, before they start spending a lot of time online. That’s why I’d like to propose adding a new course to the curriculum of every high school – one that will develop these critical thinking skills and allow teenagers to separate the wheat from the chaff in their online lives. The course will be divided into two components: critical thinking, and privacy / safety. Here is a summary of the material that would be covered:
Critical Thinking Skills
Armchair Activism: An armchair activist is someone who wants to make the world a better place – but who isn’t motivated enough to actually get out of their chair and do something about it. They spend their time sitting in front of their computer and posting (or re-posting) messages on their Facebook wall or other social media sites. Another term for this behaviour is slacktivism.

Your physics teacher will tell you that W = Fd. That is, work is equal to a force, moved across a distance. This concept also applies in the world of social media. Force can be thought of as your desire to make the world a better place. I think we all share that desire to varying degrees. However in order to accomplish any work, you need to move that force across a distance, and that means doing more than sitting in your chair and posting a message to your Facebook wall for an hour. In this course module, we’ll look at some of the popular armchair activist posts on Facebook and other social media sites, analyze them, the motivations behind them, their usefulness, what the word “support” really means, and then discuss other ways of showing our support for these causes.
Misplaced Activism: There’s an old expression, “A little knowledge is a dangerous thing”. The emphasis, of course, is on the word “little”. There are many people who want to make changes in the world, and unlike the armchair activists, they are actually willing to get out of their chairs and do something about it. However, their lack of knowledge often reduces their well-intentioned efforts to a fool’s errand or an exercise in futility. The viral nature of these widely-circulated e-mails is fascinating because they demonstrate how little the general public understands about economics and history, and how easily they can be duped. During this part of the course, we’ll take a look at some popular online boycott requests – The Great Gas Out, Procter & Gamble’s satanic imagery, Tommy Hilfiger’s xenophobia – examine their arguments, and look for any flaws in the authors’ reasoning.
Mad Skillz On The Message Boards – Identifying Logical Fallacies: Your parents’ school probably had a debate club – however, I don’t think they are as popular now. Ironically, the skills learned in debating are now almost indispensable; they will stand you in good stead when you enter the corporate world. In addition to helping you form well-structured, logical and coherent arguments, these skills will help you spot errors in your opponent’s argument. These errors are known as logical fallacies, and if you can catch your opponent using them, the you will be able to nullify his argument, deflate his ego and win the debate.

Today, similarly heated debates continue on message boards and on the reader comment sections below newspaper articles. However, not all participants are equally talented. Many people – even ones who are presumably mature and well-educated – make basic errors in defending their positions. During the next few classes, we will arm ourselves with an arsenal of devastating linguistic and logical tools, and you will learn how to deftly disarm and neutralize your message board detractors. We will also study Godwin’s Law, Confirmation Bias, the Dunning-Kreuger Effect, and how anonymity breeds hostility. Sample exercises will include:
- Identify common fallacies: straw man, ad hominem, begging the question etc.
- Analyze the reader comments sections of current news stories, and spot any flawed reasoning in the comments.
- How logical fallacies destroy your sales credibility.
Don’t Feed The Trolls: The modern-day definition of a troll is a person who posts a deliberately provocative or upsetting message to a reader comments section or message board. These people are not interested in reasoned dialogue – they simply want to get a rise out of you. It seems to be how they get their kicks.

In this unit, we will learn how to identify trolls, the methods they employ, and appropriate responses (or lack of responses) to their posts.
Spotting Shoddy Journalism: Many web sites try to pass themselves off as professional news organizations, complete with impressively-formatted web pages. They are often nothing more than a group of individuals (or members of a special interest group) who are trying to use this ruse to lend credibility to their opinions or to further some sort of political or personal agenda. In this unit, you will learn to identify credible news organizations, and recognize the hallmarks of professional journalism. For example, a domain name that contains the word “occupy” or “truth” is certainly a red flag.
Parody News Sites: A generation ago, there were only a handful of news sources, and all were completely credible: local newspapers, radio stations, television stations and news magazines. Today, you can go online and read just about any newspaper anywhere in the world, which is wonderful because you can read about world events from disparate points of view. However, there are also a growing number of parody news sources in cyberspace (and even on television), and some of their stories are so well-presented and skillfully-produced that they could easily fool novices. Some of us have a sophisticated sense of humour, and can appreciate the subtlety of a well-crafted parody news story. Unfortunately, other people will believe anything they see in print (or on a screen) that sounds the least bit plausible, and will then forward it to all of their friends.

The Daily Show with Jon Stewart is probably the best-known source of fake news and biting commentary. Online, there is The Onion, The Babylon Bee, The Beaverton, The Spoof, The Daily Mash, The Daily Currant, The Unreal Times, and Faux News. In this part of the course, we will learn the names of the most popular parody news sites, so that you’ll be able to identify them instantly. We’ll also study a number of news stories, both real and parodied, and try to determine which ones are authentic.
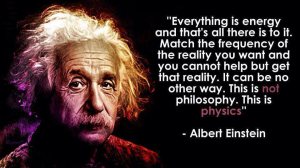
Misattributed Quotes: When your parents went to school, no one questioned the veracity of quotations. Today, anybody can post anything they want on social media, and many people don’t bother to do any research. Now we are seeing all kinds of inspirational or New Age quotes that are from a variety of unlikely sources – anyone from Einstein to Bill Cosby. How can you tell which ones are misattributed? In this unit we will examine a number of quotes (real and misattributed, with and without background images) – and discuss which ones seem authentic.
An excellent resource is the Quote Investigator web site. If you want to include a quotation in an essay or research paper, quoting someone’s Facebook post is not good enough – you need to do a little investigative work first, and provide a credible source as your reference.
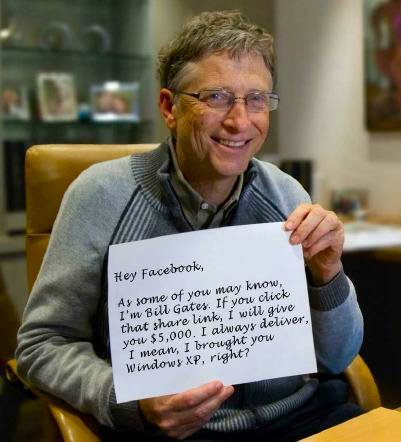
How To Spot An Urban Legend: You wouldn’t spread a rumour about someone without first checking to see if it was true… of course you wouldn’t. Unfortunately, people forward e-mail messages, re-tweet and re-post stories all the time on social media without bothering to check if the information is true. This is not done maliciously – it’s generally just because people are clueless. Many of my own middle-aged Facebook friends – many of whom are intelligent – spread urban legends because they lack the simple analytical skills to determine whether a story is false (or whether an image is Photoshopped).
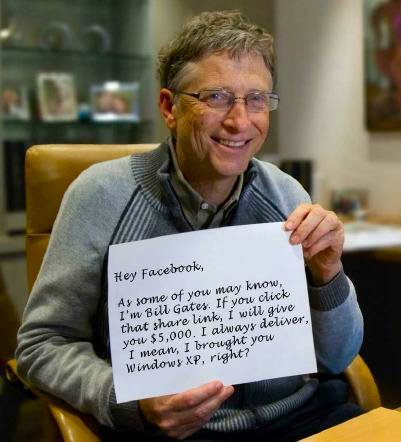
Some examples are fairly obvious – Bill Gates isn’t going to send you a cheque for $245 for forwarding a single e-mail message, but others require a little more digging to uncover their logical flaws. In this module, you will learn how to examine urban legends with a critical eye, how to spot the telltale signs, questions you should ask yourself, and several debunking resources that you can consult.
Identifying Pseudoscience: Many well-intentioned people forward official-sounding warnings about everything from artificial sweeteners to margarine, in an attempt to help us lead healthier lives. Much of this information is just utter nonsense, and will fool only those people who don’t have a solid grasp of science. In this section of the course, we’ll look at some examples, debate the merits of the author’s position, and then try to poke holes in their arguments.
Corporate E-mail Etiquette: This should be common sense, but you would be surprised by the number of young people who have lost their jobs because they didn’t behave professionally in their online communication. In this unit, we’ll look at e-mail from Claire Swire, Peter Chung, and other high-profile examples. Learn from their mistakes, and don’t let this hinder your career.
Privacy And Safety
Scam Identification: You receive an e-mail from a friend. He says that he is in England and that his wallet (containing his passport, identification, and all of his money) has been stolen. He needs you to send $1500 to a Western Union office so that he can buy a plane ticket to return home. He promises to pay you back as soon as he return. Would you send him the money? In this unit, we will discuss the various ways that people use the Internet to separate you from your money – including the Nigerian 419 scam, the European Lottery fraud, the Mystery Shopper job, and the fake Microsoft support calls.

Manage Your Online Presence: A generation ago, companies looked only at your resume when considering you for a position. Now. they will look at your LinkedIn profile, your Twitter account and even your Facebook profile. What you post online can define you as much as your resume. Practise “ego surfing”, and manage (as much as possible) what others can discover about you. Learn how to adjust your social media privacy settings and ensure that you aren’t broadcasting more about yourself than you intend to.
Photos Reveal More Than Just An Image: When you share a digital photograph, you are often sharing a lot more than just the image. Additional information, known as EXIF data, is also attached to the photo, In this unit, we’ll take a look at the EXIF data that’s saved with every photo taken with a digital camera, how it can be used to determine your exact location, and how to delete it.

No Phishing Allowed: Phishing is a technique used by hackers to get you to reveal your personal account information by pretending to be a legitimate authority or a trustworthy person. In this section of the course, we will examine common phishing attempts, and look for indicators that they are not authentic. If you receive a phishing e-mail, don’t merely delete it – there are addresses to which you can forward these e-mails so that the financial institution can take steps to identify the culprit and shut down their web site.
Online Predators: When your parents were your age, during the pre-Internet days, there was no such thing as an online predator because communication was done face-to-dace, or by telephone. A middle-aged man just couldn’t impersonate a child.

Today, everything has changed. You can be anyone you want behind you screen and some people will believe you if all they can see is words typed on a screen. This course module will teach you how to identify people who aren’t what they appear to be. Even if you don’t use this information for yourselves, teach it to your younger siblings and make them aware of the danger signs.
Online Bullying: How to identify it, and the best ways to deal with it. We will also discuss the gray area of online vigilantes – computer-savvy groups of people who identify online bullies, and then track them down and deliver their own brand of justice.
.